A High-Level Attack: Infiltration and Enigma Around an Elusive Hacker
Information
A few years ago, a sophisticated infiltration campaign shed light on the capabilities of a hacker still shrouded in mystery today, nicknamed "Jatan". Behind this pseudonym lies an actor whose mastery of personal security and concealment techniques surprised and challenged cybersecurity experts worldwide.
The attack orchestrated by Jatan ranks among the most advanced intrusion examples known to date. Rather than directly targeting the central systems of large corporations, the approach consisted of inserting into the "digital supply chain". By infecting intermediary software used by a wide range of organizations, the attackers exploited a weak point within the cybersecurity ecosystem itself. This type of attack requires meticulous planning and large-scale resources. At the same time, to avoid leaving exploitable traces, Jatan used sophisticated operational security techniques, only maintaining the bare minimum online presence to contribute to open source projects.
Despite this caution, analysts tried to learn more about Jatan and trace his potential origin. From activity data, a hypothesis formed around his time zone: UTC+8. However, inconsistencies appear when certain code changes hint at a different time zone, UTC+2 or +3. These clues suggest that Jatan might be based in Eastern Europe or the Moscow region, with a schedule more consistent with working days in a country from that region than those of China.
This particular profile and the attack structure evoke the operational methods of certain intelligence agencies, notably the APT29 group, suspected of being linked to Russian intelligence services (SVR). This resemblance to attacks such as those suffered by SolarWinds in 2020 – where management software was compromised to indirectly reach thousands of target systems – strengthens the theory that a state entity could be behind this cyber infiltration.
Since then, Jatan has erased all his online traces, but this disappearance has only fueled speculation. The expertise required to carry out an attack of this magnitude, demanding unwavering discretion for more than two years, is only within reach of highly organized groups. Many believe that other actors of equal stature, operating in the shadows, could be preparing future large-scale attacks.
This case is a reminder of how much cybersecurity has become a strategic field of action where the boundaries between individuals and states are increasingly blurred. This affair, even if it remains surrounded by mysteries, reminds us of the importance of vigilance and the continuous evolution of digital defenses to counter ever more sophisticated threats.

A High-Level Attack: Infiltration and Enigma Around an Elusive Hacker
Information
A few years ago, a sophisticated infiltration campaign shed light on the capabilities of a hacker still shrouded in mystery today, nicknamed "Jatan". Behind this pseudonym lies an actor whose mastery of personal security and concealment techniques surprised and challenged cybersecurity experts worldwide.
The attack orchestrated by Jatan ranks among the most advanced intrusion examples known to date. Rather than directly targeting the central systems of large corporations, the approach consisted of inserting into the "digital supply chain". By infecting intermediary software used by a wide range of organizations, the attackers exploited a weak point within the cybersecurity ecosystem itself. This type of attack requires meticulous planning and large-scale resources. At the same time, to avoid leaving exploitable traces, Jatan used sophisticated operational security techniques, only maintaining the bare minimum online presence to contribute to open source projects.
Despite this caution, analysts tried to learn more about Jatan and trace his potential origin. From activity data, a hypothesis formed around his time zone: UTC+8. However, inconsistencies appear when certain code changes hint at a different time zone, UTC+2 or +3. These clues suggest that Jatan might be based in Eastern Europe or the Moscow region, with a schedule more consistent with working days in a country from that region than those of China.
This particular profile and the attack structure evoke the operational methods of certain intelligence agencies, notably the APT29 group, suspected of being linked to Russian intelligence services (SVR). This resemblance to attacks such as those suffered by SolarWinds in 2020 – where management software was compromised to indirectly reach thousands of target systems – strengthens the theory that a state entity could be behind this cyber infiltration.
Since then, Jatan has erased all his online traces, but this disappearance has only fueled speculation. The expertise required to carry out an attack of this magnitude, demanding unwavering discretion for more than two years, is only within reach of highly organized groups. Many believe that other actors of equal stature, operating in the shadows, could be preparing future large-scale attacks.
This case is a reminder of how much cybersecurity has become a strategic field of action where the boundaries between individuals and states are increasingly blurred. This affair, even if it remains surrounded by mysteries, reminds us of the importance of vigilance and the continuous evolution of digital defenses to counter ever more sophisticated threats.

A High-Level Attack: Infiltration and Enigma Around an Elusive Hacker
Information
A few years ago, a sophisticated infiltration campaign shed light on the capabilities of a hacker still shrouded in mystery today, nicknamed "Jatan". Behind this pseudonym lies an actor whose mastery of personal security and concealment techniques surprised and challenged cybersecurity experts worldwide.
The attack orchestrated by Jatan ranks among the most advanced intrusion examples known to date. Rather than directly targeting the central systems of large corporations, the approach consisted of inserting into the "digital supply chain". By infecting intermediary software used by a wide range of organizations, the attackers exploited a weak point within the cybersecurity ecosystem itself. This type of attack requires meticulous planning and large-scale resources. At the same time, to avoid leaving exploitable traces, Jatan used sophisticated operational security techniques, only maintaining the bare minimum online presence to contribute to open source projects.
Despite this caution, analysts tried to learn more about Jatan and trace his potential origin. From activity data, a hypothesis formed around his time zone: UTC+8. However, inconsistencies appear when certain code changes hint at a different time zone, UTC+2 or +3. These clues suggest that Jatan might be based in Eastern Europe or the Moscow region, with a schedule more consistent with working days in a country from that region than those of China.
This particular profile and the attack structure evoke the operational methods of certain intelligence agencies, notably the APT29 group, suspected of being linked to Russian intelligence services (SVR). This resemblance to attacks such as those suffered by SolarWinds in 2020 – where management software was compromised to indirectly reach thousands of target systems – strengthens the theory that a state entity could be behind this cyber infiltration.
Since then, Jatan has erased all his online traces, but this disappearance has only fueled speculation. The expertise required to carry out an attack of this magnitude, demanding unwavering discretion for more than two years, is only within reach of highly organized groups. Many believe that other actors of equal stature, operating in the shadows, could be preparing future large-scale attacks.
This case is a reminder of how much cybersecurity has become a strategic field of action where the boundaries between individuals and states are increasingly blurred. This affair, even if it remains surrounded by mysteries, reminds us of the importance of vigilance and the continuous evolution of digital defenses to counter ever more sophisticated threats.
 Hindi
Hindi  French
French  English
English  Spanish
Spanish  Chinese
Chinese  Japanese
Japanese  Korean
Korean  German
German 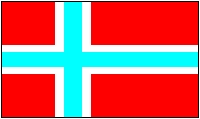 Norwegian
Norwegian